**** UPDATE 6/27/2015: As of the App Catalog Shutdown, this method will no longer work!! ****
With the HP App Catalog shutting down soon, now is the time to grab offline copies of any of the apps you’ve installed or purchased.
This method will use your devices’ existing credentials to grab a list of all the apps you’ve purchased/installed, and download each one from HPs servers before they are shutdown.
First, we need to get a few things off of our WebOS device. You will need the Preware app “Impostah” in order to complete these steps. Go to each relevant page and email the info to yourself.
- Open Impostah
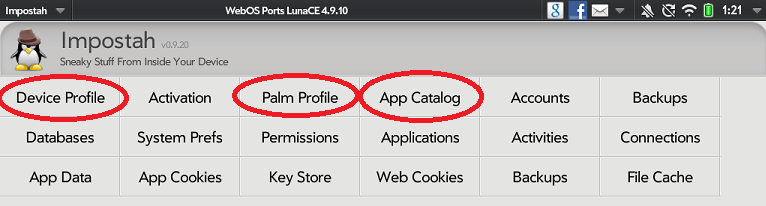
- Tap “Palm Profile”
- Tap “Show Palm Profile”
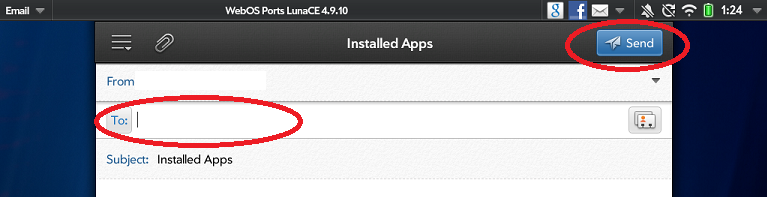
- Tap the Impostah menu (upper left) and choose “Email”

- Put in your email address and hit “Send”
- Go back to Impostah home
- Repeat email steps (4 and 5) for “Device Profile -> Show Device Profile”
- Repeat email steps (4 and 5) for “App Catalog -> Show Installed Apps”
Now, we’ve gathered the required information, we’ll need to get the script ready to run on our own computer.
- Dowload the script from here: https://github.com/PrplHaz4/webos-ipk-dump/blob/1.2/webos-ipk-dump.zip?raw=true
- Open the downloaded webos-ipk-dump.zip file
- Extract the files to c:\temp
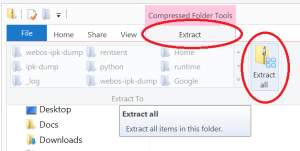

- You should now see webos-ipk-dump.exe inside c:\temp\webos-ipk-dump directory
- Double-click “webos-ipk-dump” folder to see its contents (should contain a .exe file)
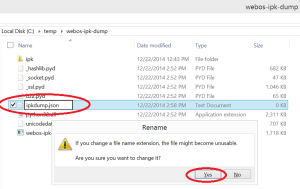
- Right click on a blank space in the folder and choose “New -> Text Document”
- Rename “New Text Document.txt” to ipkdump.json (click “yes” to change the file name extension)
- Find the email you sent yourself earlier with “Installed Apps”
- Copy the entire email BODY (from the first “{” to the last “}”)
- Paste it into the blank Notepad document
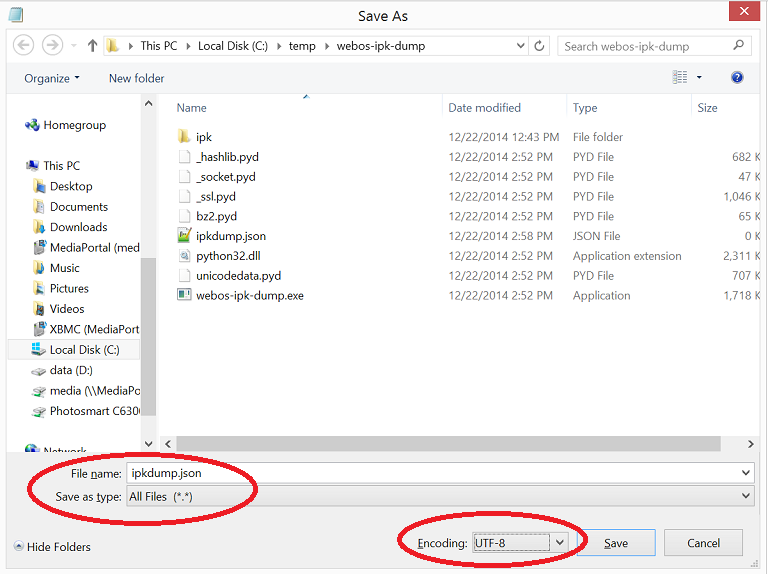
- Notepad -> File -> Save As…
- Give it a name “ipkdump.json
- Select Save as type: All Files (*.*)
- Encoding: UTF-8 (THIS IS VERY IMPORTANT!)
- Save
Everything is all set up, and we are ready to run the script!
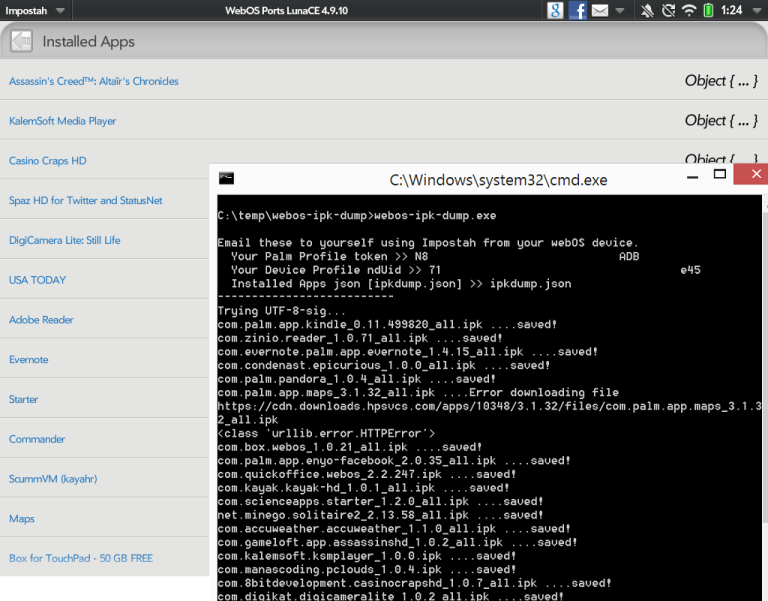
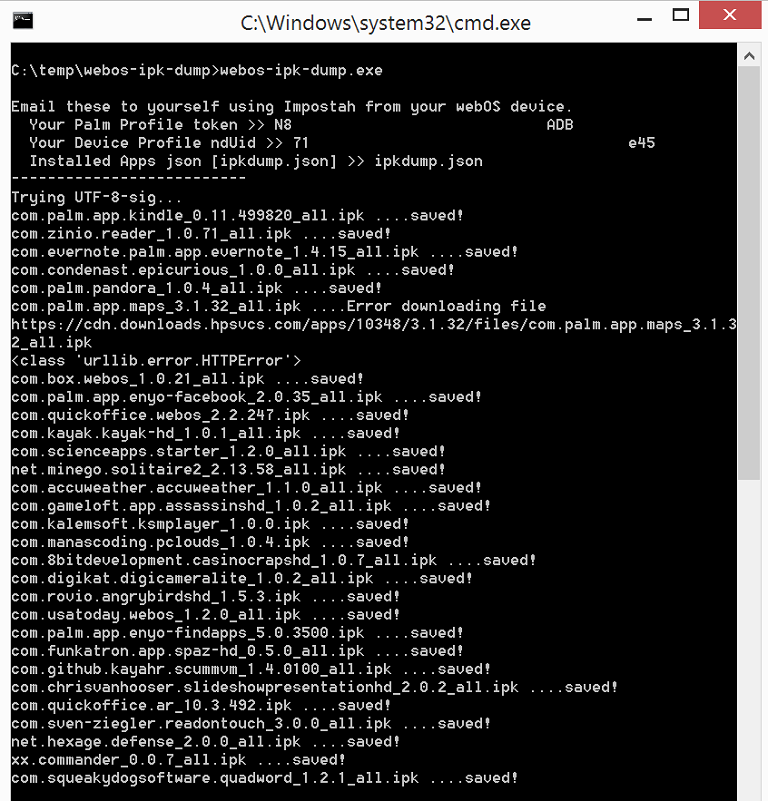
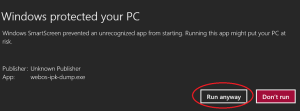
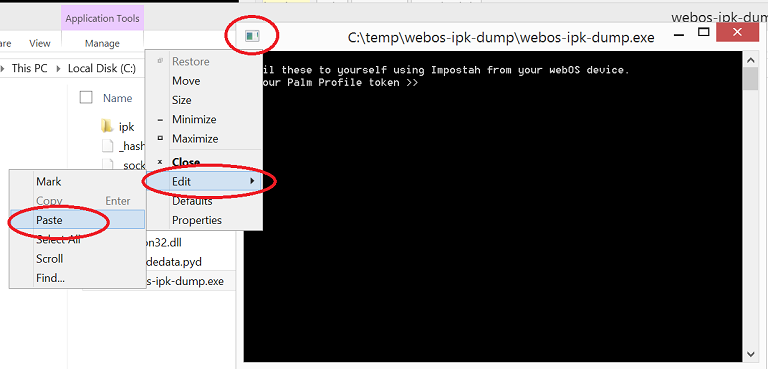
- Double-click “webos-ipk-dump.exe”
- If prompted with a Windows protection dialog, click “More Info -> Run Anyway”
- You should see a command line application come up
- Go back to the email you sent called “Palm Profile”
- Find and copy the “token” value to your clipboard (just the long string of numbers)
"token": "
NXXX7A12XXXA1432XXX7D0XXXF3EXXXDB", - Paste it into the script when you’re asked for “Palm Profile Token” (hit enter)
- Go back to the last email you sent called “Device Profile”
- Find and copy the “nduId” value to your clipboard (for devices with cellular radios – Pre, Veer, 4G…etc – use the IMEI instead of nduId)
"nduId": "
7xxx47axxxcd3xxx2a6exxxa20dxxxb4a3cxxx45", - Paste it into the script when you’re asked for “Device Profile nduId” (hit enter)
- Type ipkdump.json for the “Installed Apps json” (hit enter)
- Your downloads show start immediately – some apps are larger than others so may take a long time to download
You’re done. You can find the your downloaded apps in the folder:
c:\temp\webos-ipk-dump\ipk
** If you cancel the processing for whatever reason, be sure to delete the last downloaded file, as it will be an incomplete download!
Notes:
Windows Notepad file encoding (or JSON/Python)
ANSI fails
Unicode works (UTF-16)
Unicode Big-endian works (UTF-16)
UTF-8 works (UTF-8-SIG) *preferred